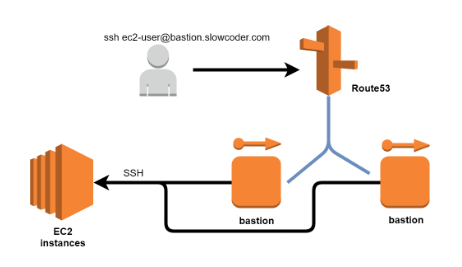
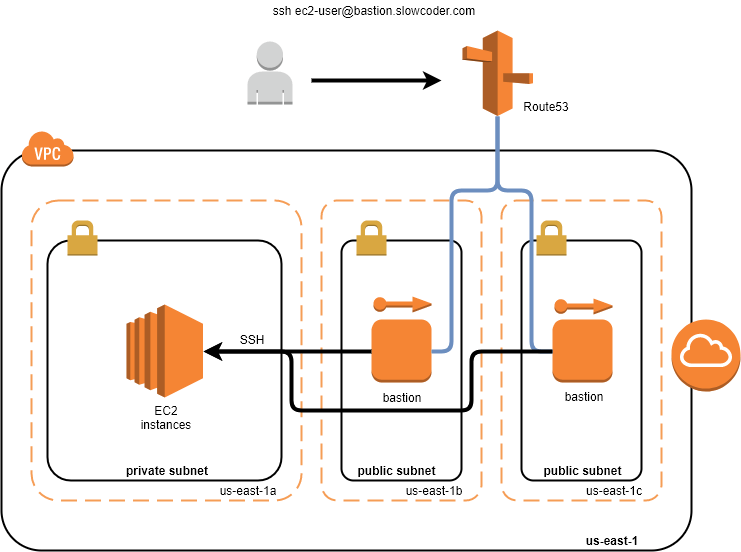
Instances in a private subnet don’t have a public IP address, and without a VPN or a DirectConnect option, Bastion Host (JumpBox) is the expected mechanism to reach your servers. Therefore, we should make it Highly Available.
In this quick post, I will show you how to setup a Highly Available Bastion Hosts with the following targets :
- Bastion hosts will be deployed in two Availability Zones to support immediate access across the VPC & withstand an AZ failure.
- Elastic IP addresses are associated with the bastion instances to make sure the same trusted Elastic IPs are used at all times.
- Bastion Hosts will be reachable via a permanent DNS entry configured with Route53.
In order to easily setup the infrastructure described above, I used Terraform:
1 | git clone https://github.com/mlabouardy/terraform-aws-labs |
Note: I did a tutorial on how to the setup a VPC with Terraform so make sure to read it for more details.
Update the variables.tfvars file with your SSH Key Pair name and an existing Hosted Zone ID. Then, issue the following command:
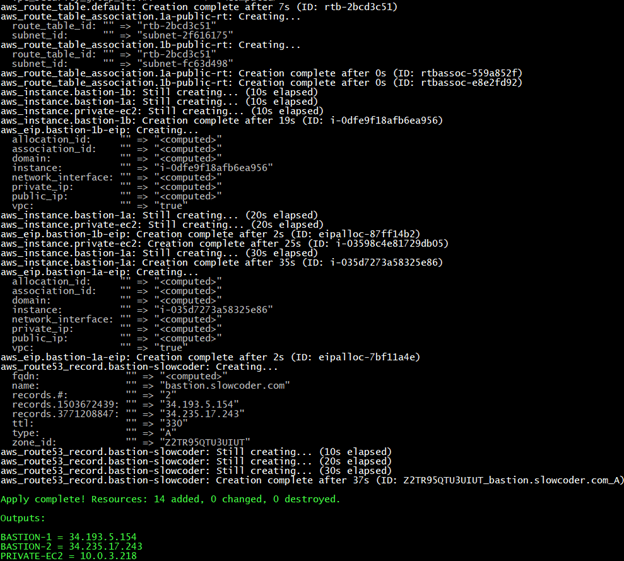
1 | terraform apply -var-file=variables.tfvars |
That will bring up the VPC, and all the necessary resources:
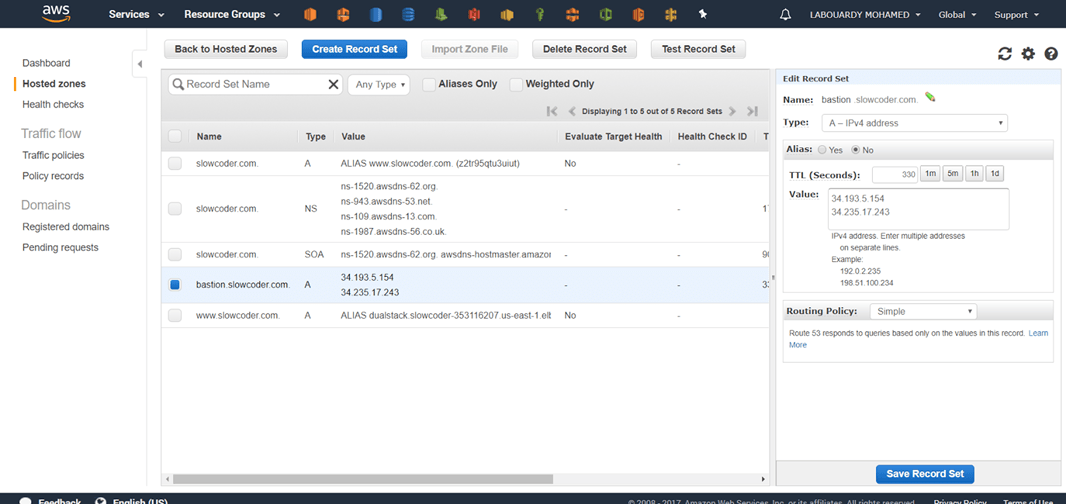
Now in your AWS Management Console you should see the resources created:
EC2 Instances:

DNS Record:
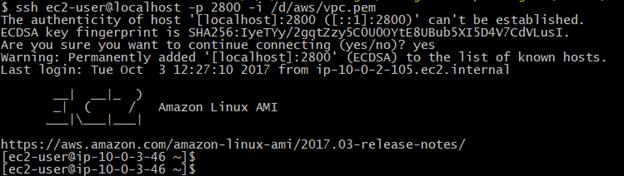
Finally, create an SSH tunnel using the DNS record to your private instance:
1 | ssh -f ec2-user@bastion.slowcoder.com -i /d/aws/vpc.pem -L 2800:10.0.3.218:22 -N |
Once done, you should now be able to access to your private instances via SSH:
1 | ssh ec2-user@localhost -p 2800 -i /d/aws/vpc.pem |
Take it further ? instead of defining number of bastion hosts, we could use a bastion host inside an autoscaling group with min target set to 1.
Drop your comments, feedback, or suggestions below — or connect with me directly on Twitter @mlabouardy.